#include <winpr/config.h>#include <winpr/assert.h>#include "ntlm.h"#include "../sspi.h"#include <winpr/crt.h>#include <winpr/sam.h>#include <winpr/ntlm.h>#include <winpr/print.h>#include <winpr/crypto.h>#include <winpr/sysinfo.h>#include "ntlm_compute.h"#include "../../log.h"Macros | |
| #define | TAG WINPR_TAG("sspi.NTLM") |
| #define | NTLM_CheckAndLogRequiredCapacity(tag, s, nmemb, what) |
Variables | |
| static char | NTLM_CLIENT_SIGN_MAGIC [] = "session key to client-to-server signing key magic constant" |
| static char | NTLM_SERVER_SIGN_MAGIC [] = "session key to server-to-client signing key magic constant" |
| static char | NTLM_CLIENT_SEAL_MAGIC [] = "session key to client-to-server sealing key magic constant" |
| static char | NTLM_SERVER_SEAL_MAGIC [] = "session key to server-to-client sealing key magic constant" |
| static const BYTE | NTLM_NULL_BUFFER [16] |
Macro Definition Documentation
◆ NTLM_CheckAndLogRequiredCapacity
| #define NTLM_CheckAndLogRequiredCapacity | ( | tag, | |
| s, | |||
| nmemb, | |||
| what | |||
| ) |
◆ TAG
| #define TAG WINPR_TAG("sspi.NTLM") |
WinPR: Windows Portable Runtime NTLM Security Package (Compute)
Copyright 2011-2014 Marc-Andre Moreau marcandre.moreau@gmail.com
Licensed under the Apache License, Version 2.0 (the "License"); you may not use this file except in compliance with the License. You may obtain a copy of the License at
http://www.apache.org/licenses/LICENSE-2.0
Unless required by applicable law or agreed to in writing, software distributed under the License is distributed on an "AS IS" BASIS, WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied. See the License for the specific language governing permissions and limitations under the License.
Function Documentation
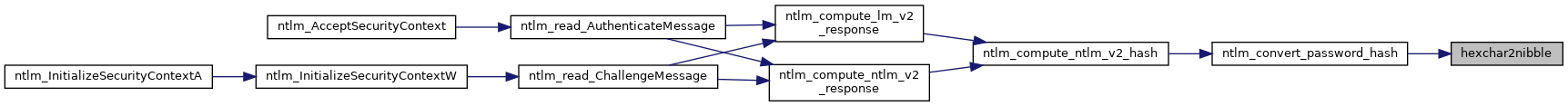
◆ hexchar2nibble()
|
static |
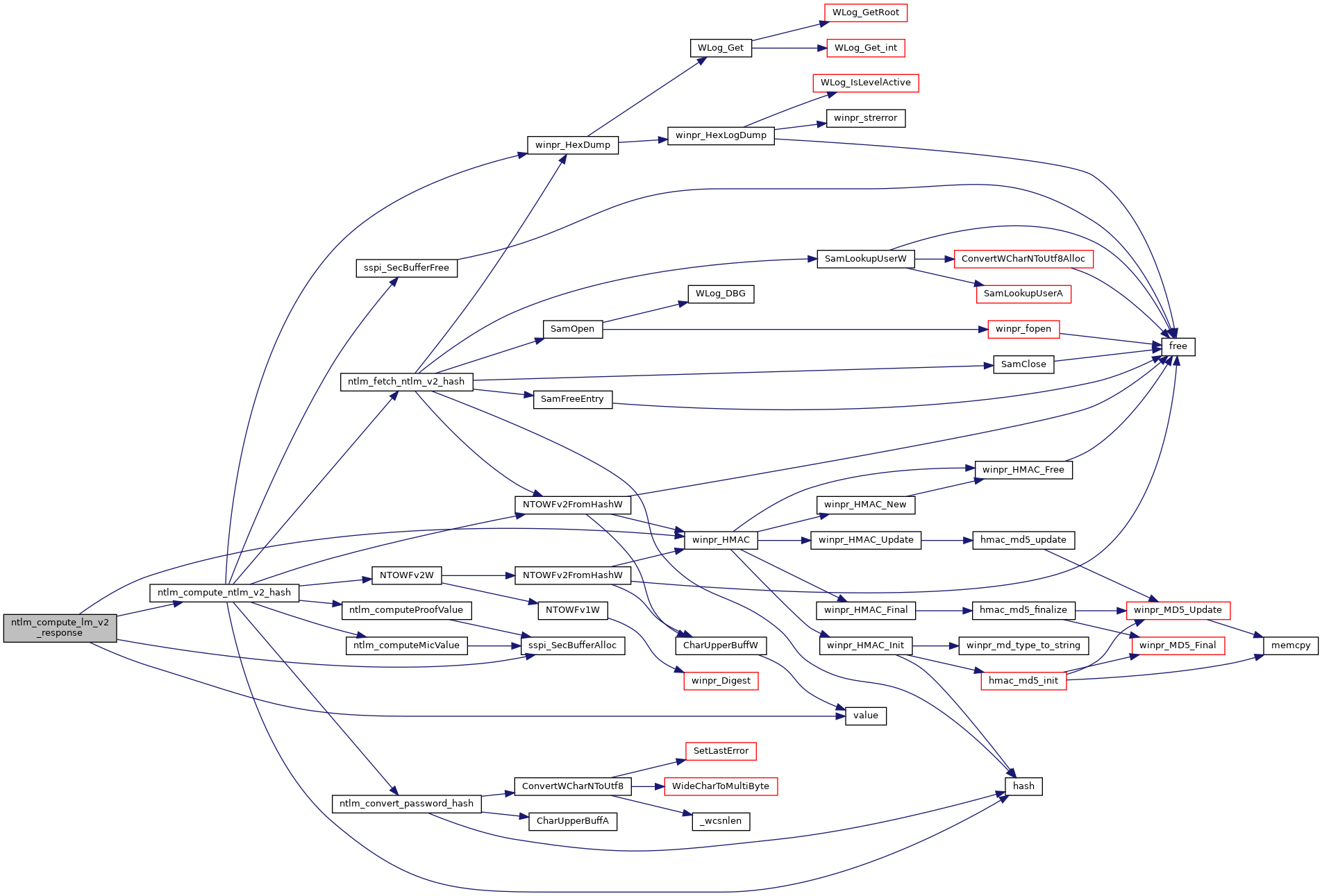
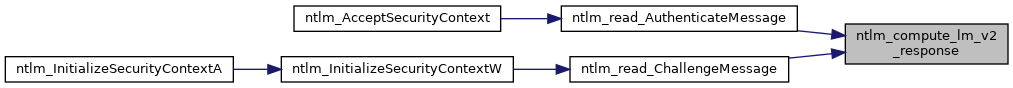
◆ ntlm_compute_lm_v2_response()
| BOOL ntlm_compute_lm_v2_response | ( | NTLM_CONTEXT * | context | ) |
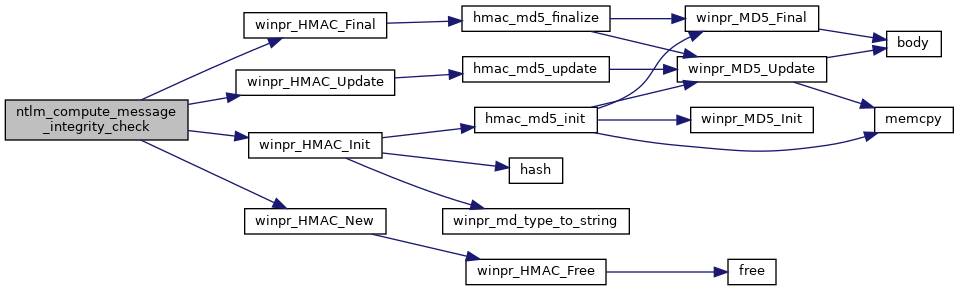
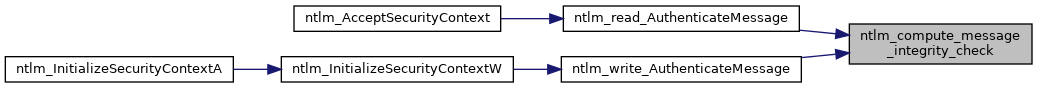
◆ ntlm_compute_message_integrity_check()
| BOOL ntlm_compute_message_integrity_check | ( | NTLM_CONTEXT * | context, |
| BYTE * | mic, | ||
| UINT32 | size | ||
| ) |
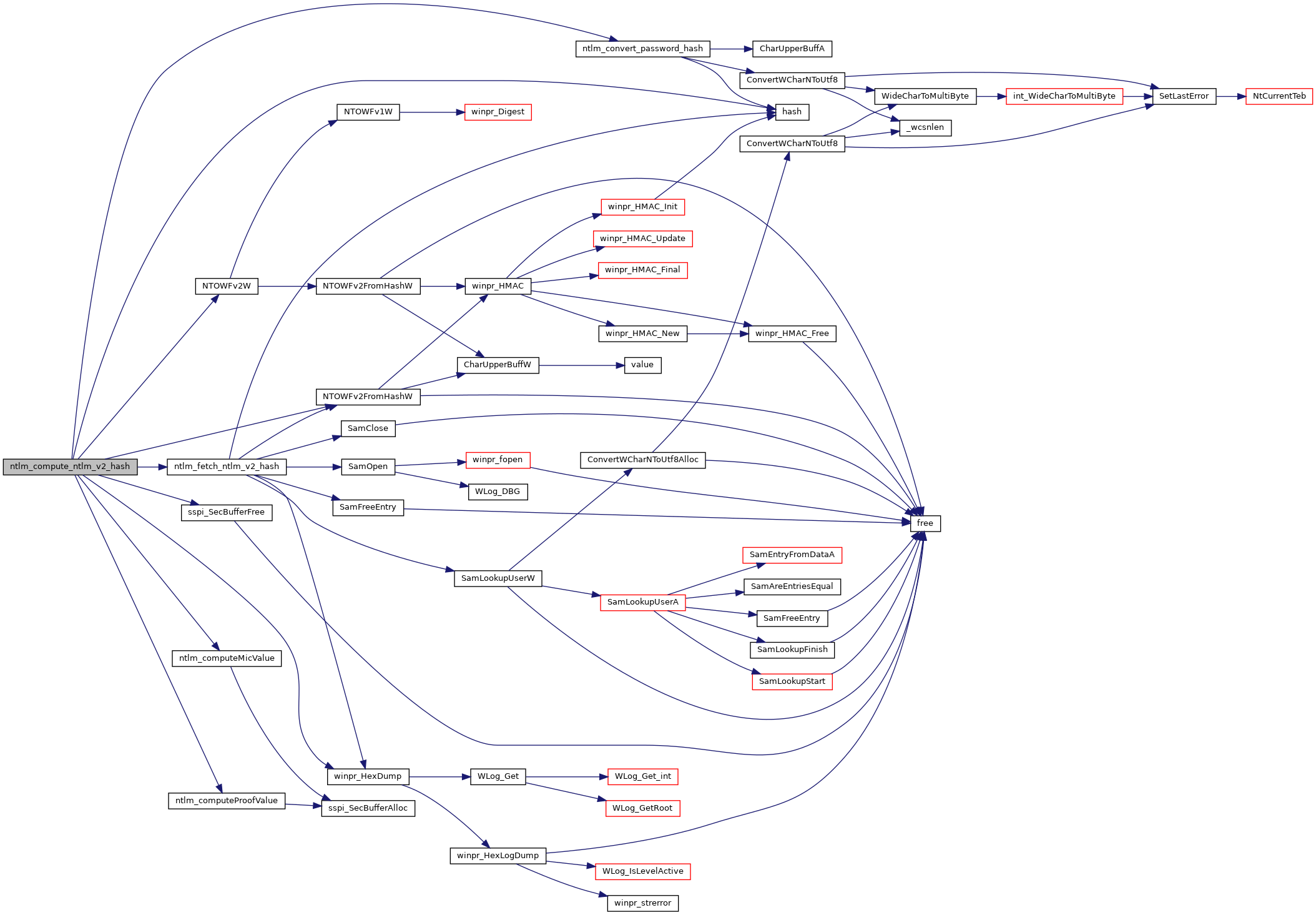
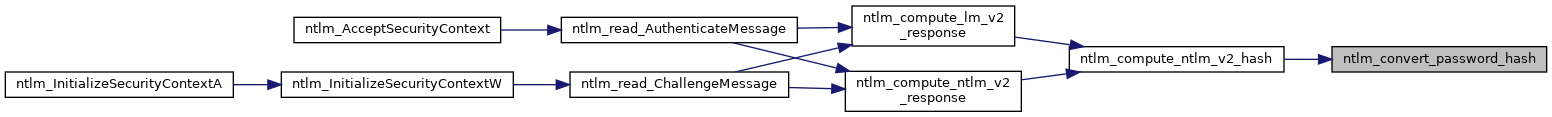
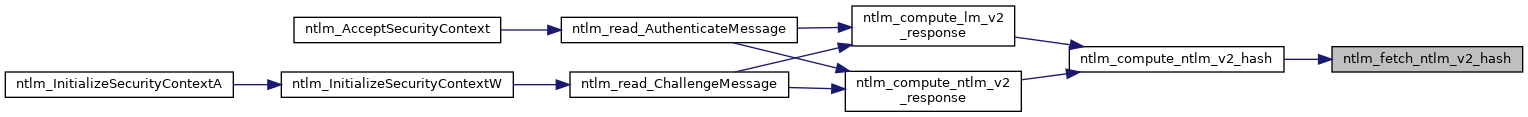
◆ ntlm_compute_ntlm_v2_hash()
|
static |
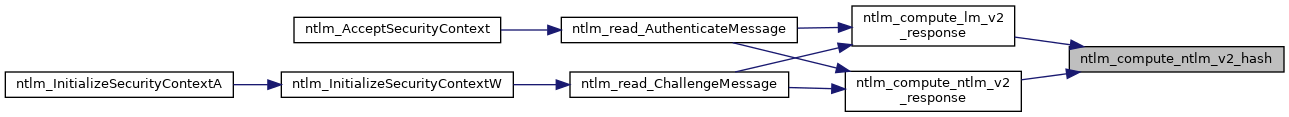
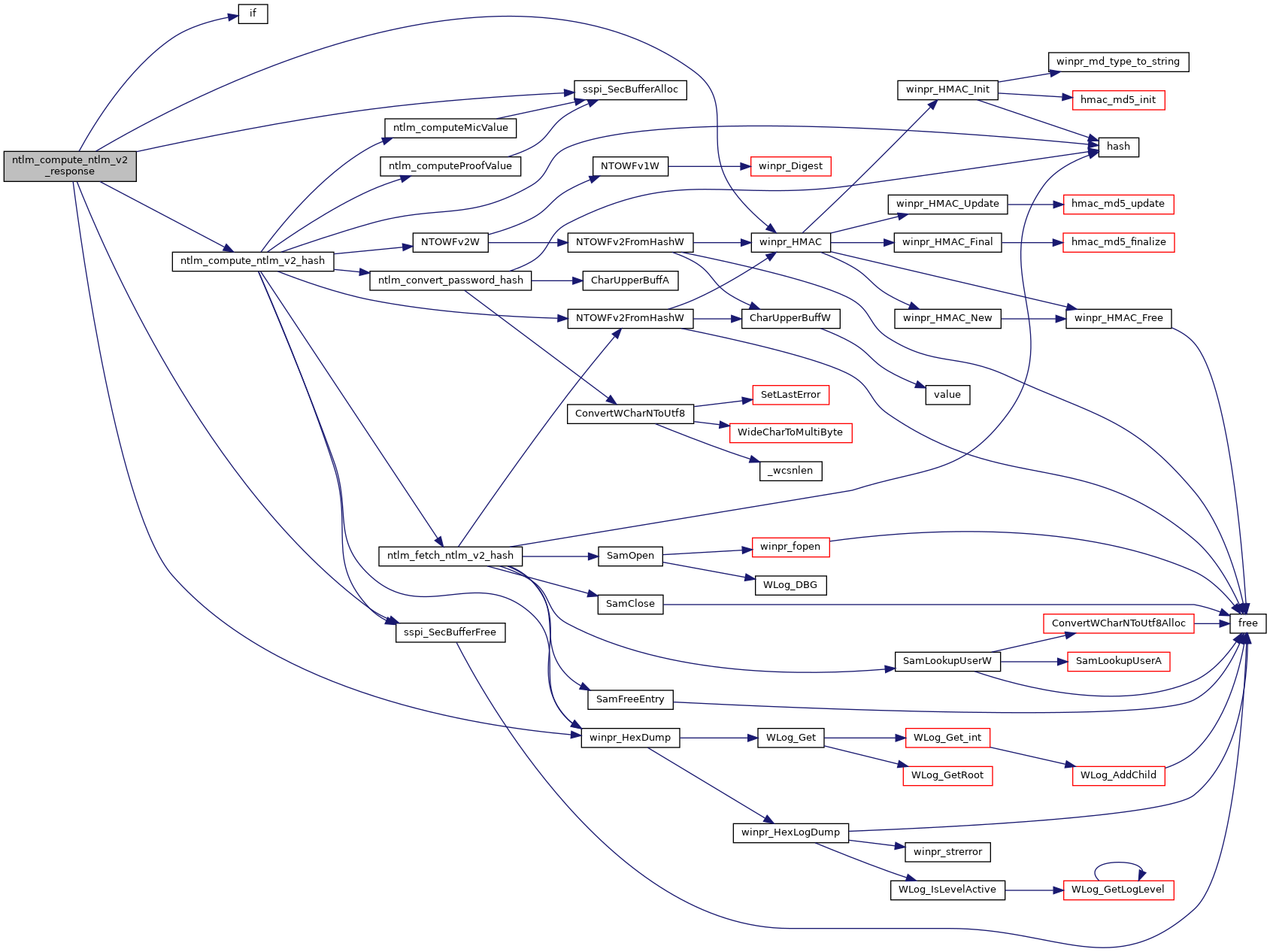
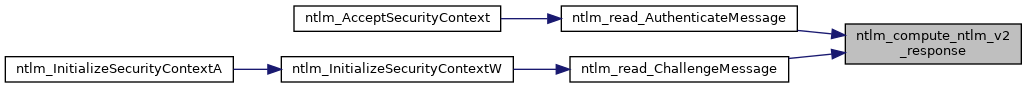
◆ ntlm_compute_ntlm_v2_response()
| BOOL ntlm_compute_ntlm_v2_response | ( | NTLM_CONTEXT * | context | ) |
Compute NTLMv2 Response.
NTLMv2_RESPONSE msdn{cc236653} NTLMv2 Authentication msdn{cc236700}
- Parameters
-
context A pointer to the NTLM context
- Returns
- TRUE for success, FALSE for failure
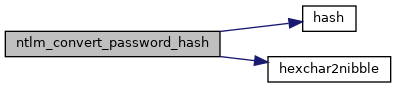
◆ ntlm_convert_password_hash()
|
static |
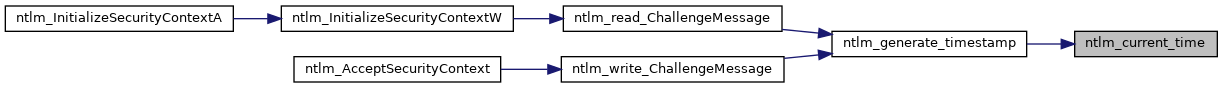
◆ ntlm_current_time()
| void ntlm_current_time | ( | BYTE * | timestamp | ) |
Get current time, in tenths of microseconds since midnight of January 1, 1601.
- Parameters
-
[out] timestamp 64-bit little-endian timestamp

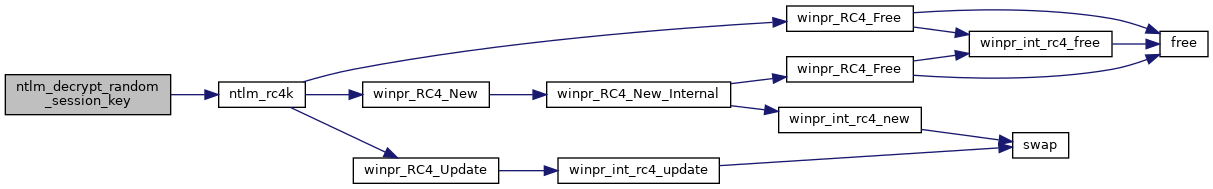
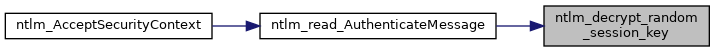
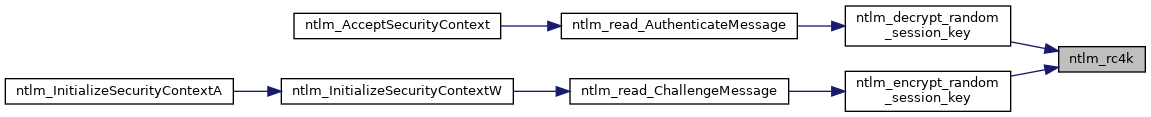
◆ ntlm_decrypt_random_session_key()
| void ntlm_decrypt_random_session_key | ( | NTLM_CONTEXT * | context | ) |
Decrypt RandomSessionKey (RC4-encrypted RandomSessionKey, using KeyExchangeKey as the key).
- Parameters
-
context A pointer to the NTLM context
if (NegotiateFlags & NTLMSSP_NEGOTIATE_KEY_EXCH)
Set RandomSessionKey to RC4K(KeyExchangeKey,
AUTHENTICATE_MESSAGE.EncryptedRandomSessionKey) else Set RandomSessionKey to KeyExchangeKey
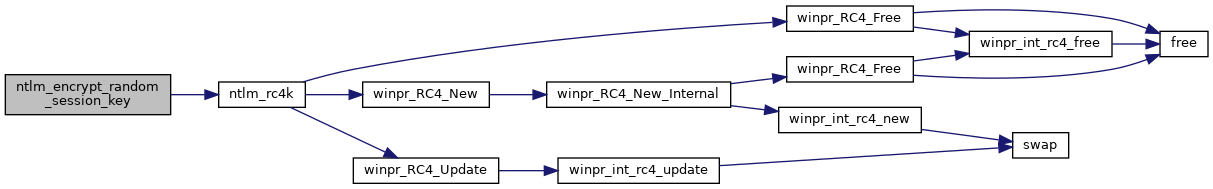
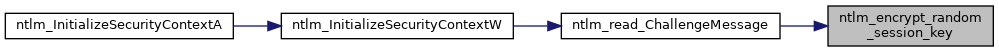
◆ ntlm_encrypt_random_session_key()
| void ntlm_encrypt_random_session_key | ( | NTLM_CONTEXT * | context | ) |
Encrypt RandomSessionKey (RC4-encrypted RandomSessionKey, using KeyExchangeKey as the key).
- Parameters
-
context A pointer to the NTLM context
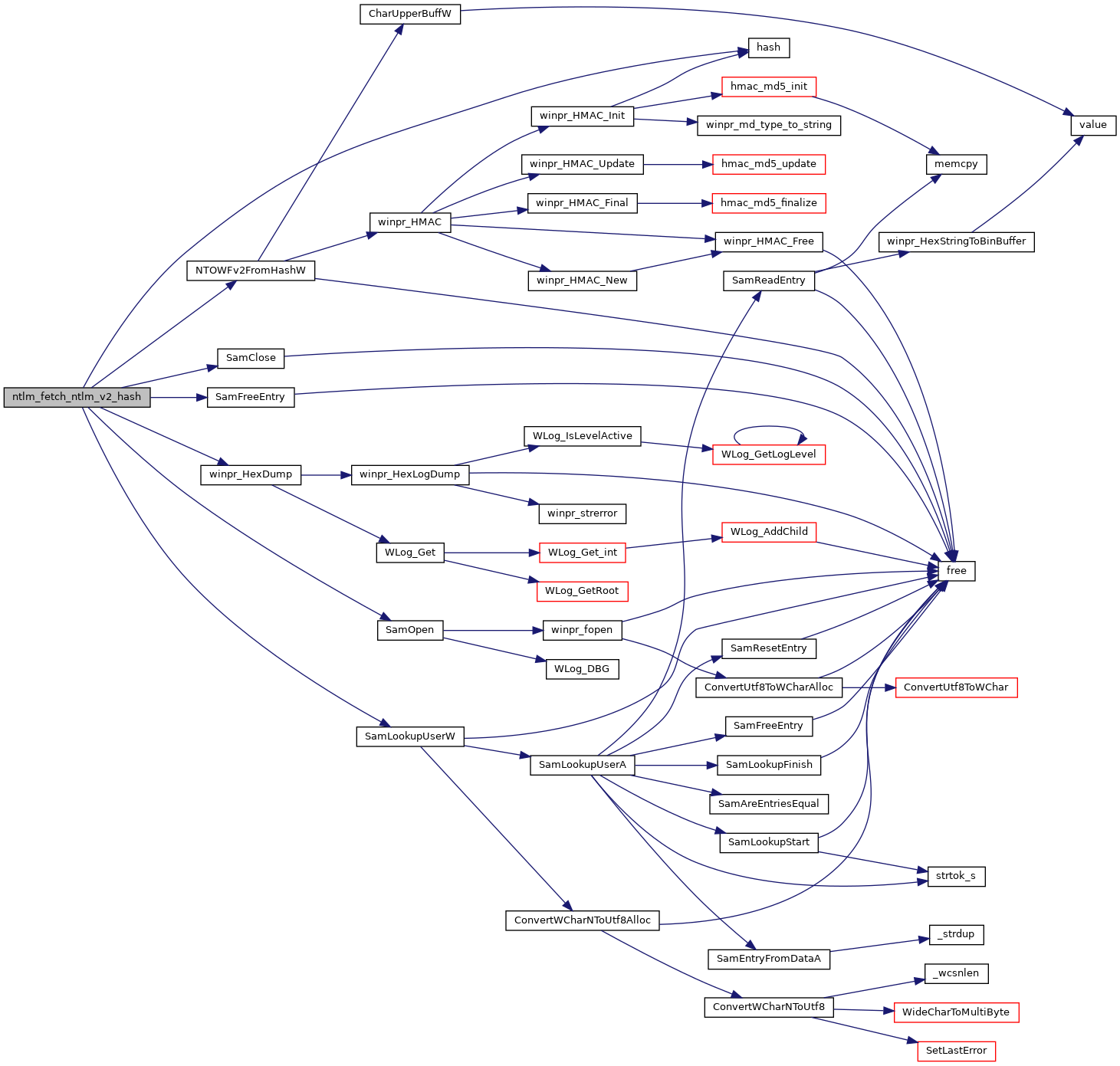
◆ ntlm_fetch_ntlm_v2_hash()
|
static |
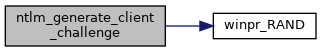
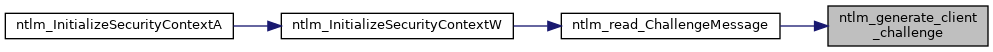
◆ ntlm_generate_client_challenge()
| void ntlm_generate_client_challenge | ( | NTLM_CONTEXT * | context | ) |
Generate client challenge (8-byte nonce).
- Parameters
-
context A pointer to the NTLM context
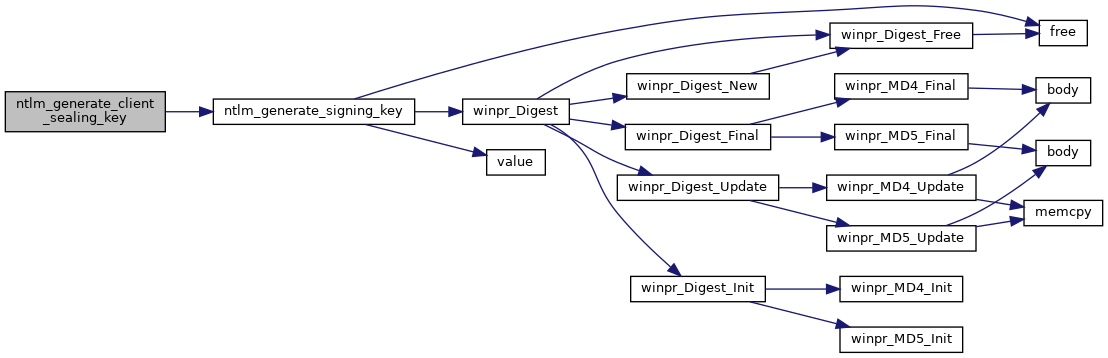
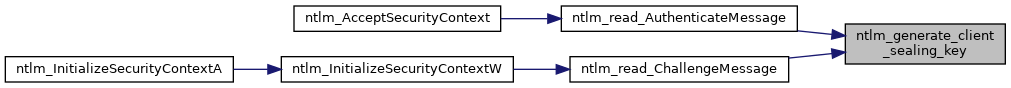
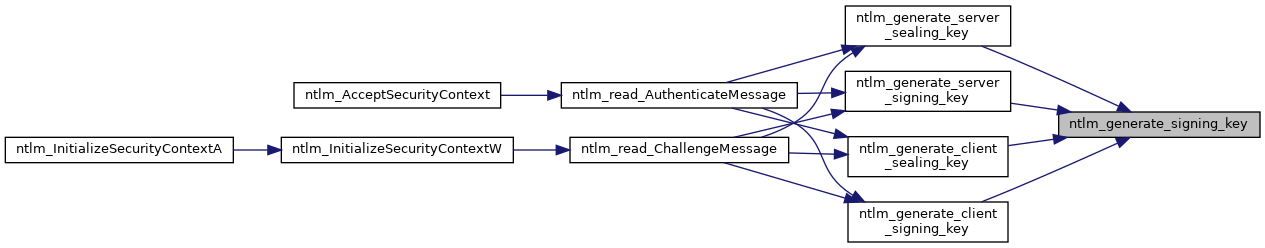
◆ ntlm_generate_client_sealing_key()
| BOOL ntlm_generate_client_sealing_key | ( | NTLM_CONTEXT * | context | ) |
Generate client sealing key (ClientSealingKey). msdn{cc236712}
- Parameters
-
context A pointer to the NTLM context
- Returns
- TRUE for success, FALSE for failure
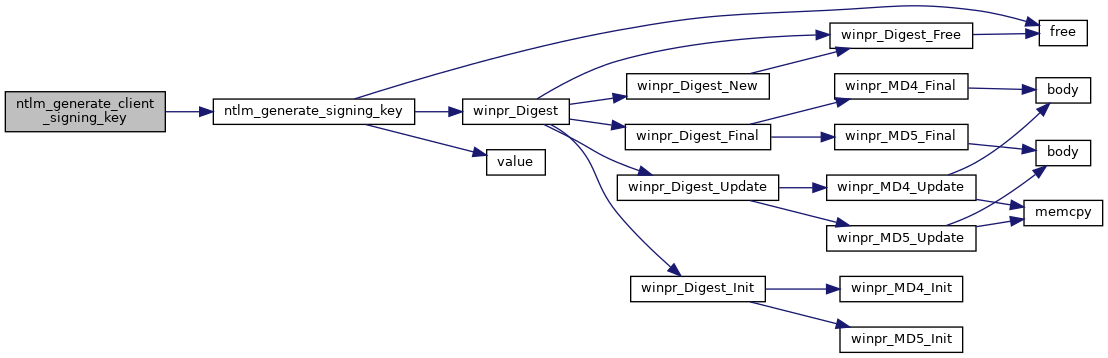
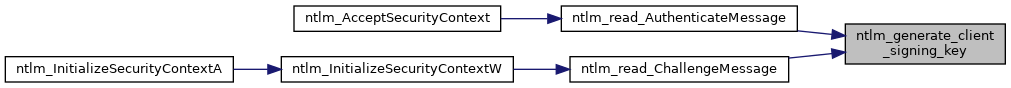
◆ ntlm_generate_client_signing_key()
| BOOL ntlm_generate_client_signing_key | ( | NTLM_CONTEXT * | context | ) |
Generate client signing key (ClientSigningKey). msdn{cc236711}
- Parameters
-
context A pointer to the NTLM context
- Returns
- TRUE for success, FALSE for failure
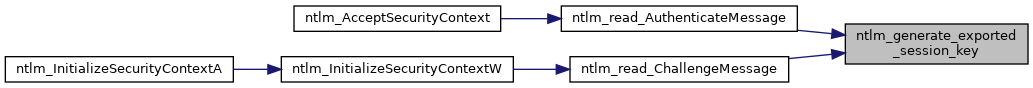
◆ ntlm_generate_exported_session_key()
| void ntlm_generate_exported_session_key | ( | NTLM_CONTEXT * | context | ) |
Generate ExportedSessionKey (the RandomSessionKey, exported)
- Parameters
-
context A pointer to the NTLM context
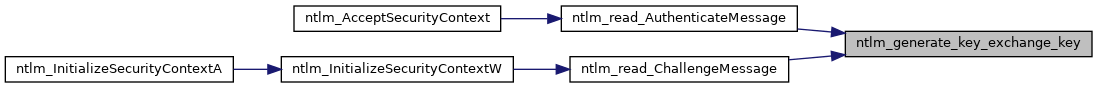
◆ ntlm_generate_key_exchange_key()
| void ntlm_generate_key_exchange_key | ( | NTLM_CONTEXT * | context | ) |
Generate KeyExchangeKey (the 128-bit SessionBaseKey). msdn{cc236710}
- Parameters
-
context A pointer to the NTLM context
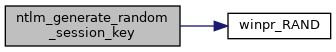
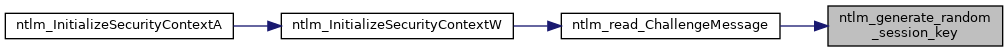
◆ ntlm_generate_random_session_key()
| void ntlm_generate_random_session_key | ( | NTLM_CONTEXT * | context | ) |
Generate RandomSessionKey (16-byte nonce).
- Parameters
-
context A pointer to the NTLM context
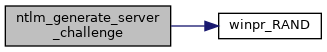
◆ ntlm_generate_server_challenge()
| void ntlm_generate_server_challenge | ( | NTLM_CONTEXT * | context | ) |
Generate server challenge (8-byte nonce).
- Parameters
-
context A pointer to the NTLM context
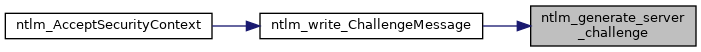
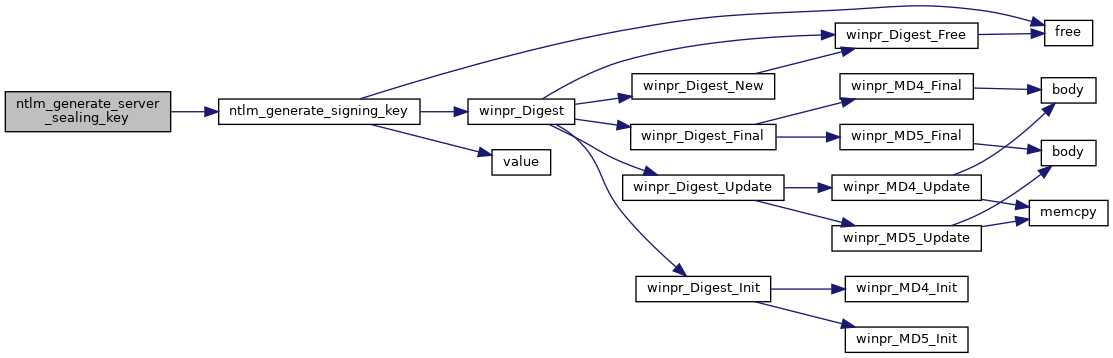
◆ ntlm_generate_server_sealing_key()
| BOOL ntlm_generate_server_sealing_key | ( | NTLM_CONTEXT * | context | ) |
Generate server sealing key (ServerSealingKey). msdn{cc236712}
- Parameters
-
context A pointer to the NTLM context
- Returns
- TRUE for success, FALSE for failure
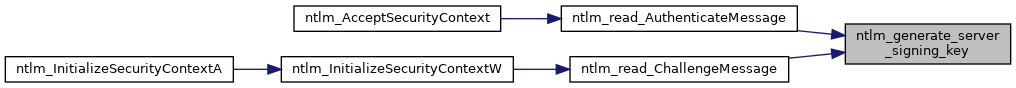
◆ ntlm_generate_server_signing_key()
| BOOL ntlm_generate_server_signing_key | ( | NTLM_CONTEXT * | context | ) |
Generate server signing key (ServerSigningKey). msdn{cc236711}
- Parameters
-
context A pointer to the NTLM context
- Returns
- TRUE for success, FALSE for failure
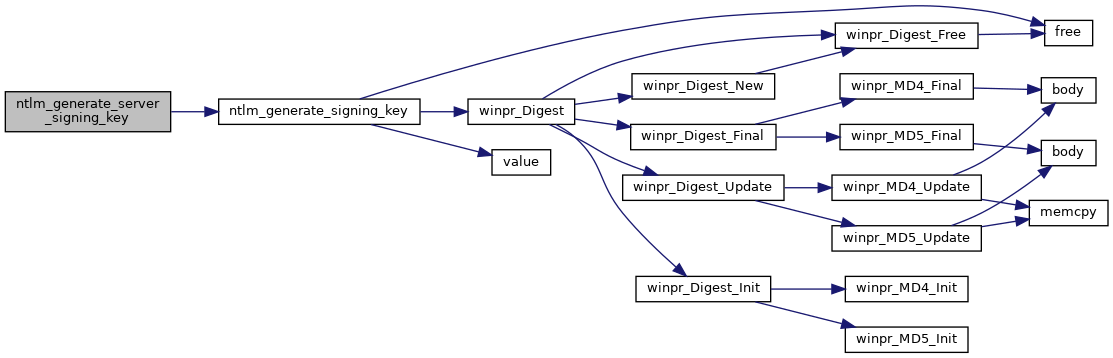
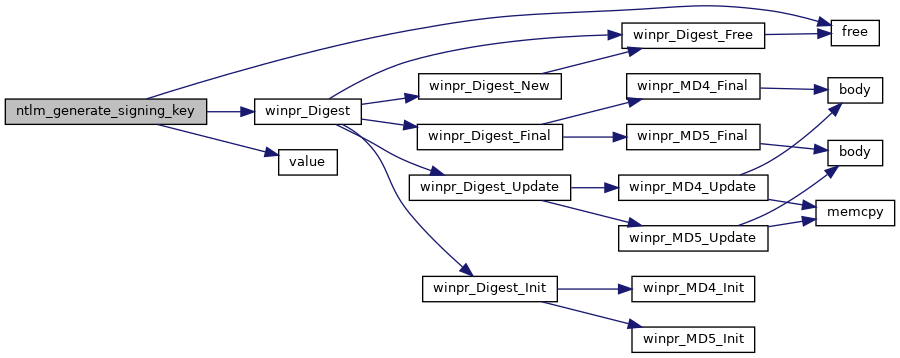
◆ ntlm_generate_signing_key()
|
static |
Generate signing key msdn{cc236711}
- Parameters
-
exported_session_key ExportedSessionKey sign_magic Sign magic string signing_key Destination signing key
- Returns
- TRUE for success, FALSE for failure
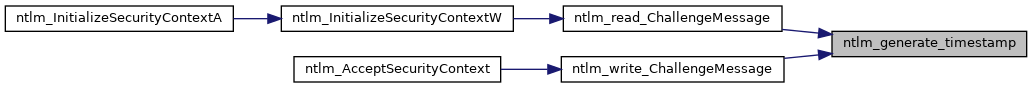
◆ ntlm_generate_timestamp()
| void ntlm_generate_timestamp | ( | NTLM_CONTEXT * | context | ) |
Generate timestamp for AUTHENTICATE_MESSAGE.
- Parameters
-
context A pointer to the NTLM context

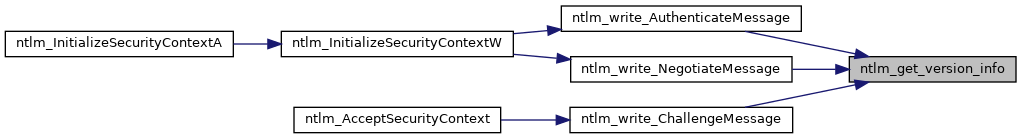
◆ ntlm_get_version_info()
| BOOL ntlm_get_version_info | ( | NTLM_VERSION_INFO * | versionInfo | ) |
Populate VERSION structure msdn{cc236654}
- Parameters
-
versionInfo A pointer to the version struct
- Returns
- TRUE for success, FALSE for failure
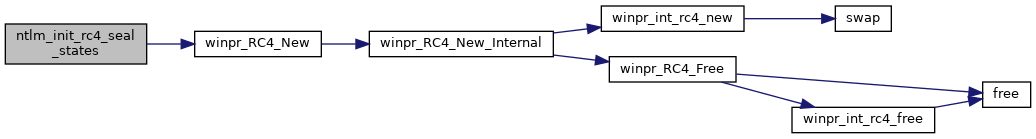
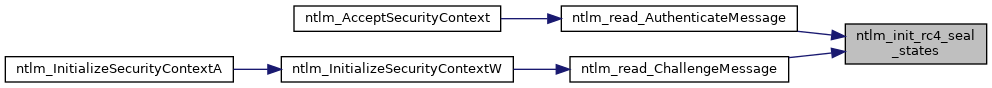
◆ ntlm_init_rc4_seal_states()
| BOOL ntlm_init_rc4_seal_states | ( | NTLM_CONTEXT * | context | ) |
Initialize RC4 stream cipher states for sealing.
- Parameters
-
context A pointer to the NTLM context
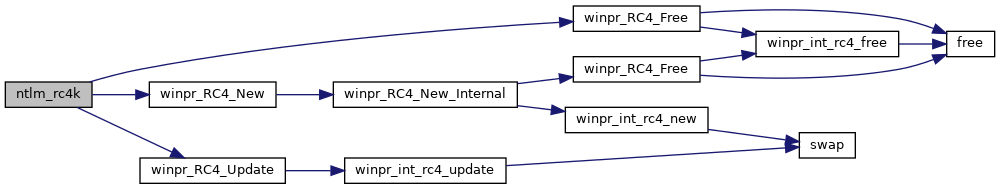
◆ ntlm_rc4k()
Encrypt the given plain text using RC4 and the given key.
- Parameters
-
key RC4 key length text length plaintext plain text ciphertext cipher text
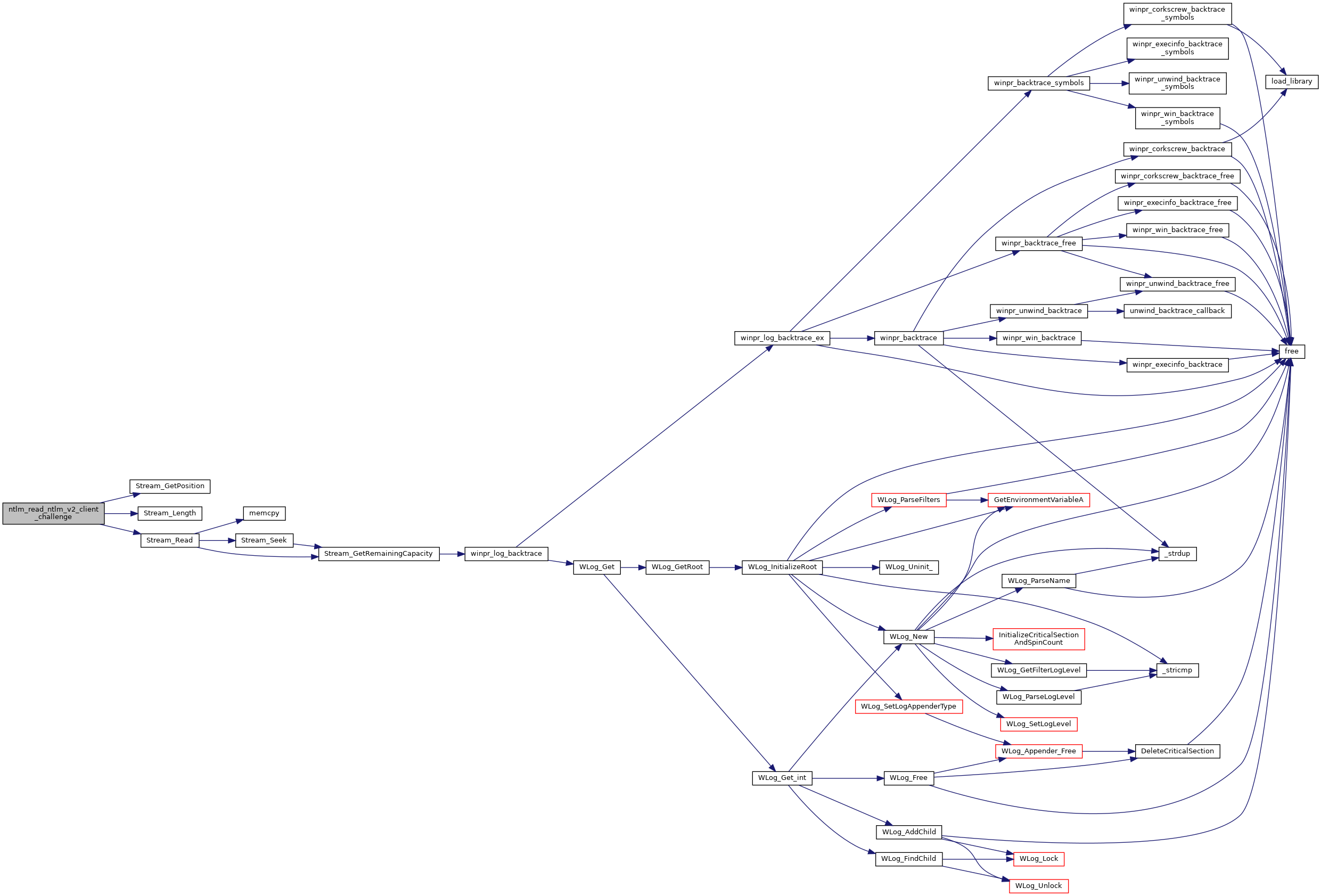
◆ ntlm_read_ntlm_v2_client_challenge()
|
static |
Print VERSION structure. msdn{cc236654}
- Parameters
-
versionInfo A pointer to the struct containing the data to print
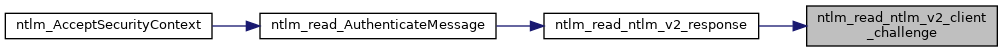
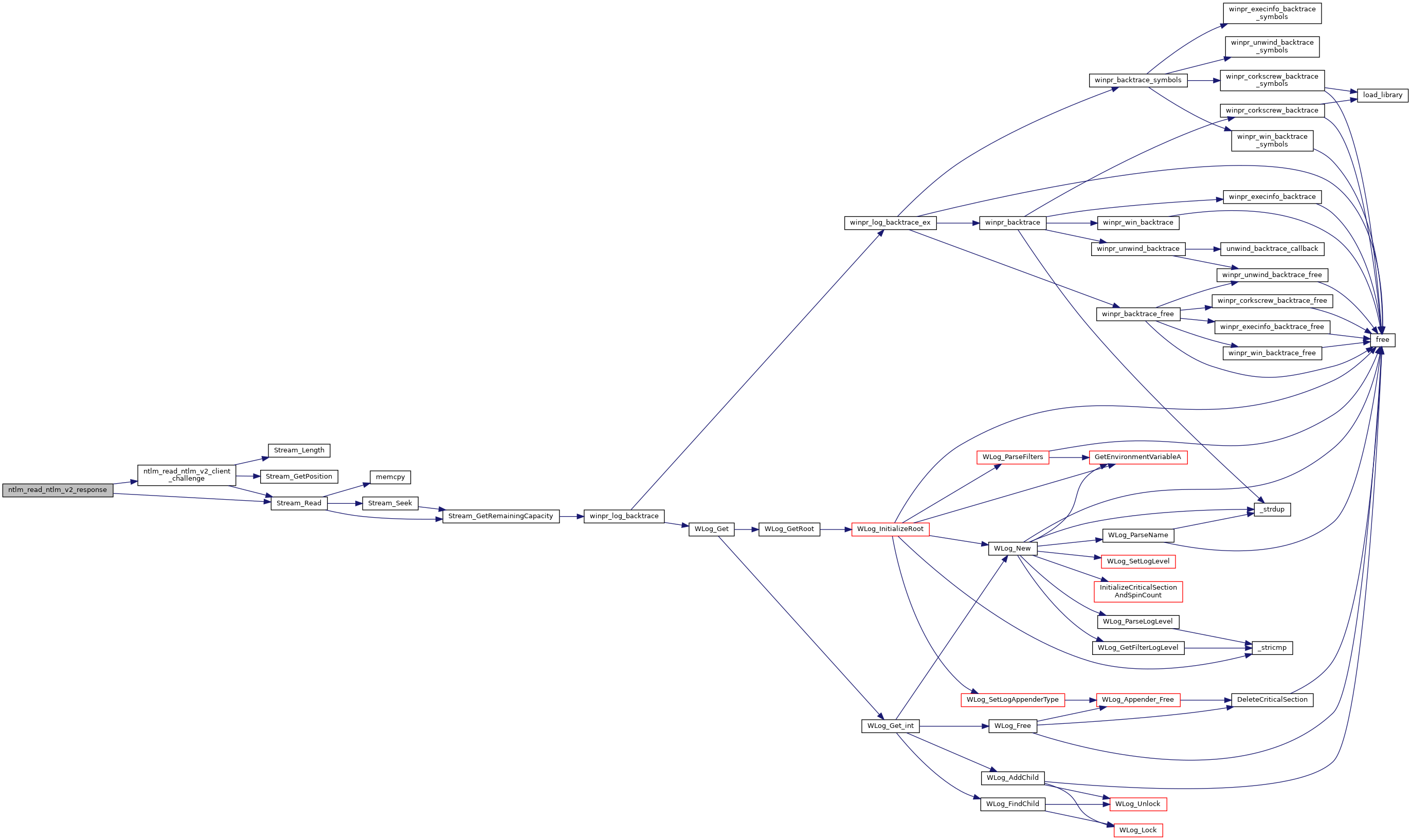
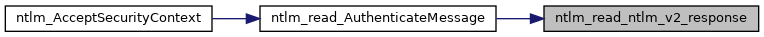
◆ ntlm_read_ntlm_v2_response()
| BOOL ntlm_read_ntlm_v2_response | ( | wStream * | s, |
| NTLMv2_RESPONSE * | response | ||
| ) |
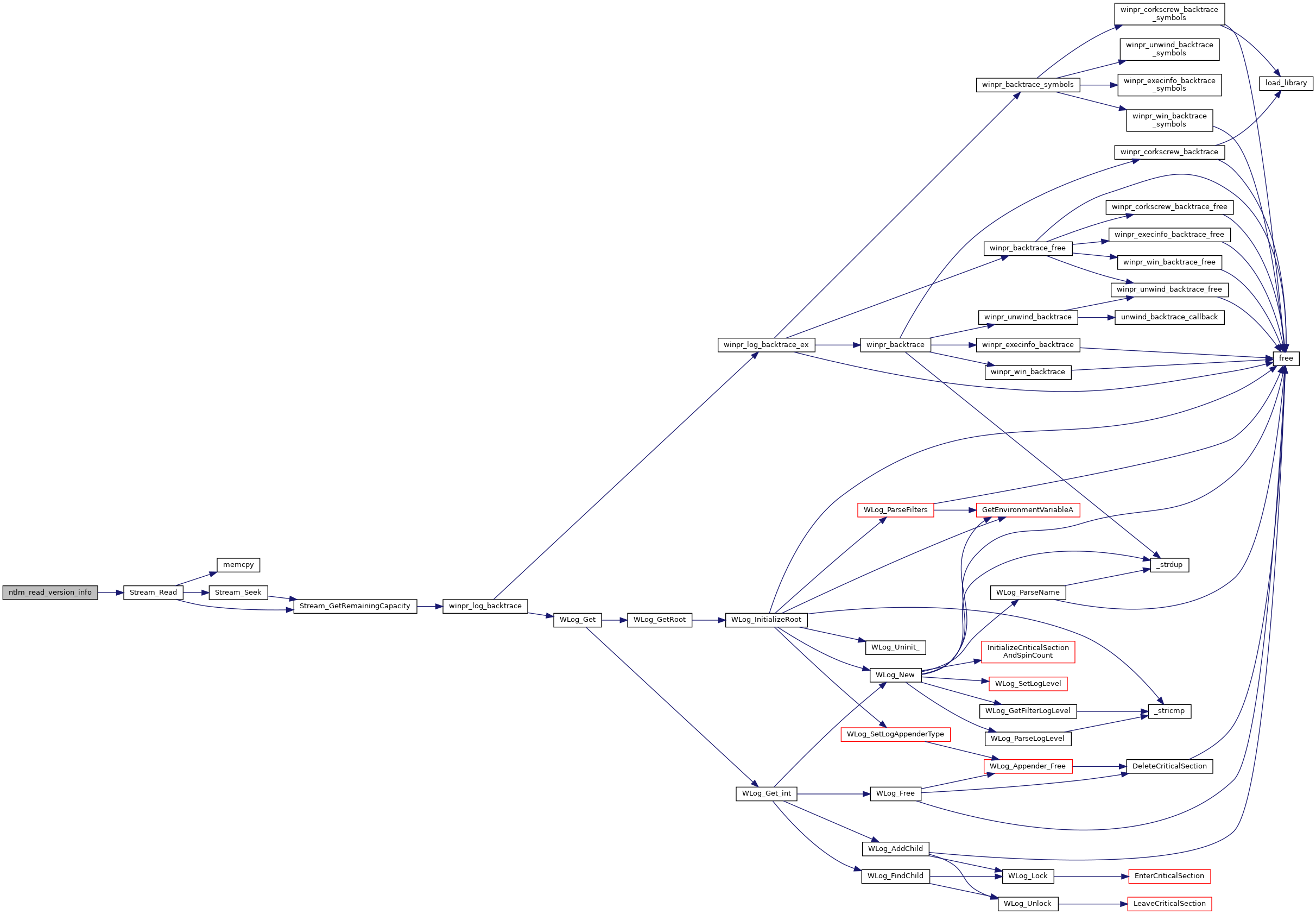
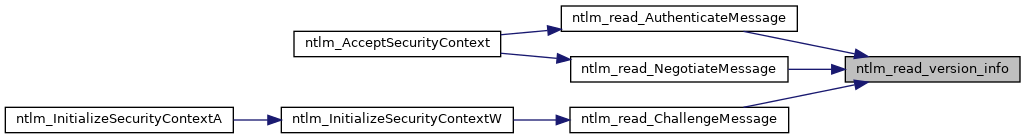
◆ ntlm_read_version_info()
| BOOL ntlm_read_version_info | ( | wStream * | s, |
| NTLM_VERSION_INFO * | versionInfo | ||
| ) |
Read VERSION structure. msdn{cc236654}
- Parameters
-
s A pointer to a stream to read versionInfo A pointer to the struct to read data to
- Returns
- TRUE for success, FALSE for failure
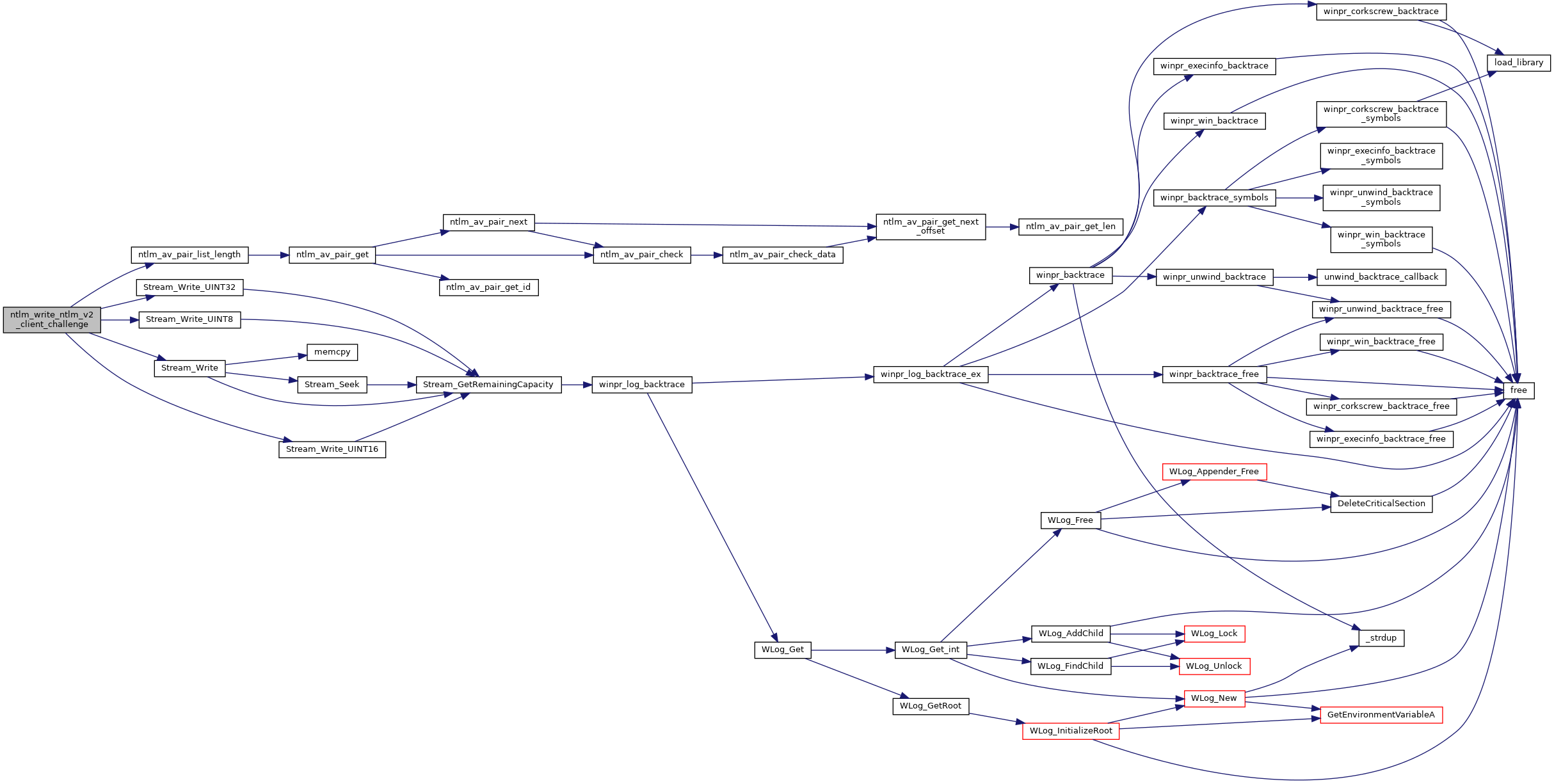
◆ ntlm_write_ntlm_v2_client_challenge()
|
static |
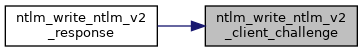
◆ ntlm_write_ntlm_v2_response()
| BOOL ntlm_write_ntlm_v2_response | ( | wStream * | s, |
| const NTLMv2_RESPONSE * | response | ||
| ) |
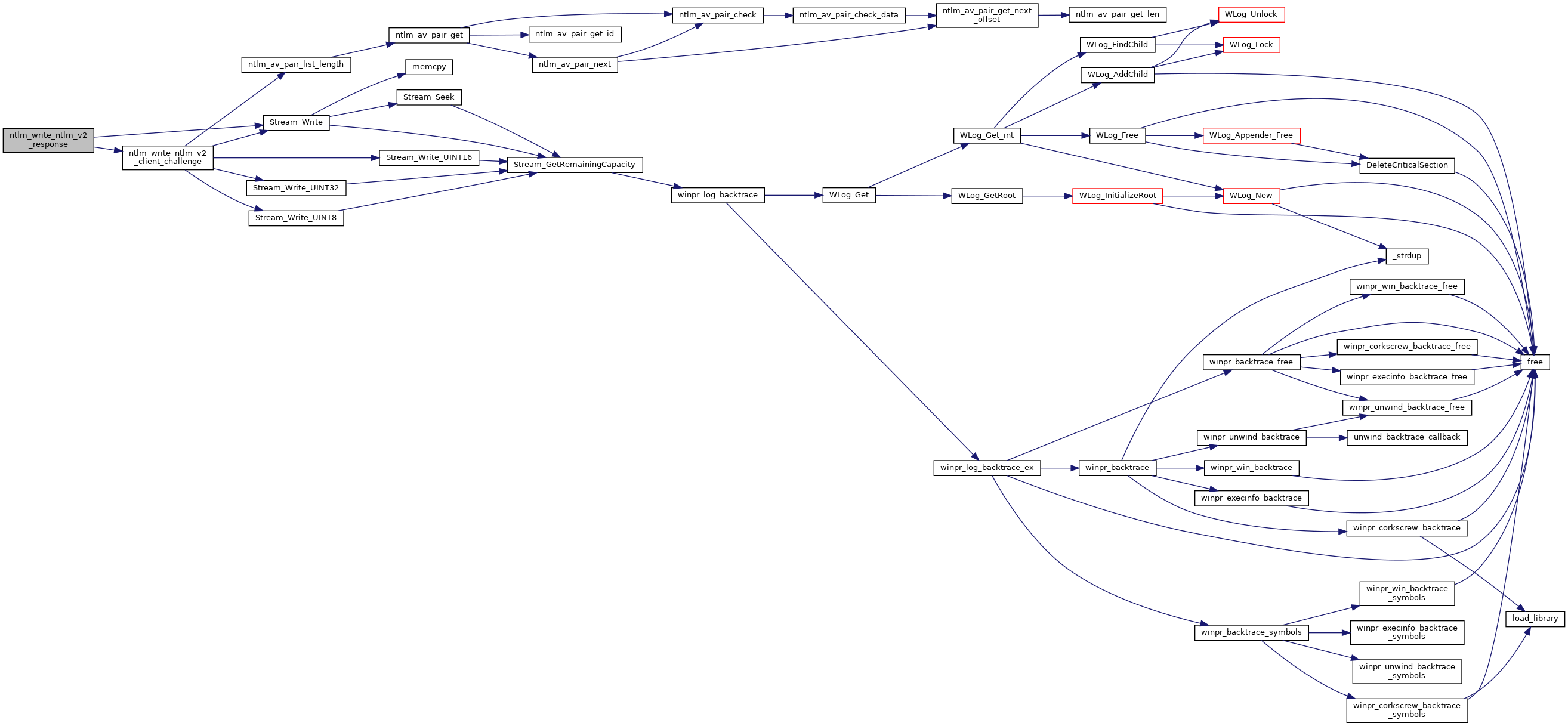
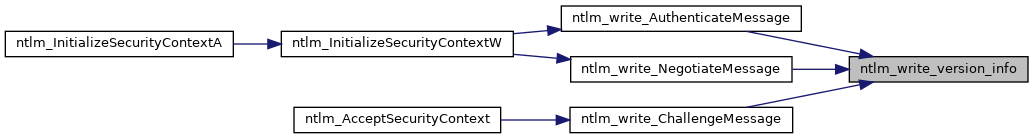
◆ ntlm_write_version_info()
| BOOL ntlm_write_version_info | ( | wStream * | s, |
| const NTLM_VERSION_INFO * | versionInfo | ||
| ) |
Write VERSION structure. msdn{cc236654}
- Parameters
-
s A pointer to the stream to write to versionInfo A pointer to the buffer to read the data from
- Returns
- TRUE for success, FALSE for failure
Variable Documentation
◆ NTLM_CLIENT_SEAL_MAGIC
|
static |
◆ NTLM_CLIENT_SIGN_MAGIC
|
static |
◆ NTLM_NULL_BUFFER
|
static |
◆ NTLM_SERVER_SEAL_MAGIC
|
static |
◆ NTLM_SERVER_SIGN_MAGIC
|
static |